Anti-forgery token prevents CSRF (Cross-Site Request Forgery) attacks. The server associates this token with current user’s identity and sends it to the client. In the next request from client, the server expects to see this token. If the token is missing or it is different, then the server rejects the request (Reference).
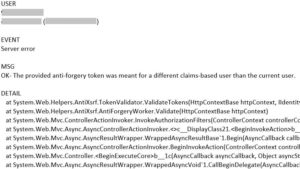
I have recently worked on some anti-forgery related errors. These are the error messages I saw in Event Viewer:
The provided anti-forgery token was meant for a different claims-based user than the current user.
The provided anti-forgery token was meant for user “”, but the current user is “X”.
The anti-forgery cookie token and form field token do not match.
The required anti-forgery cookie “__RequestVerificationToken” is not present.