An ASP.NET WebForms project adds several scripts to the page on the fly. Since these scripts don’t exist in the compile time, how to whitelist these dynamic scripts with CSP?
The title and the first paragraph may sound pretty abstract. Let’s look at the fundamentals first.
Are you receiving “Custom JavaScript is not allowed” error? Check this post out.
What is CSP (Content Security Policy)?
CSP is an HTTP header that we use to prevent cross site scripting (XSS) and packet sniffing attacks. Long story short: By using CSP header, we tell the browser which scripts or other resources we trust. The browser executes these resources and ignores the rest.
Here is an example CSP header:
object-src 'none'; script-src 'nonce-{random}' 'unsafe-inline'As mentioned in this article, this header means:
object-src 'none'Prevents fetching and executing plugin resources embedded using<object>,<embed>or<applet>tags. The most common example is Flash.
script-src nonce-{random} 'unsafe-inline'Thenoncedirective means that<script>elements will be allowed to execute only if they contain a nonce attribute matching the randomly-generated value which appears in the policy.Note: In the presence of a CSP nonce the
unsafe-inlinedirective will be ignored by modern browsers. Older browsers, which don’t support nonces, will seeunsafe-inlineand allow inline scripts to execute.
For more information about CSP:
- Official reference
- W3C specification
- Mozilla documentation
- A Google tool to query CSP headers
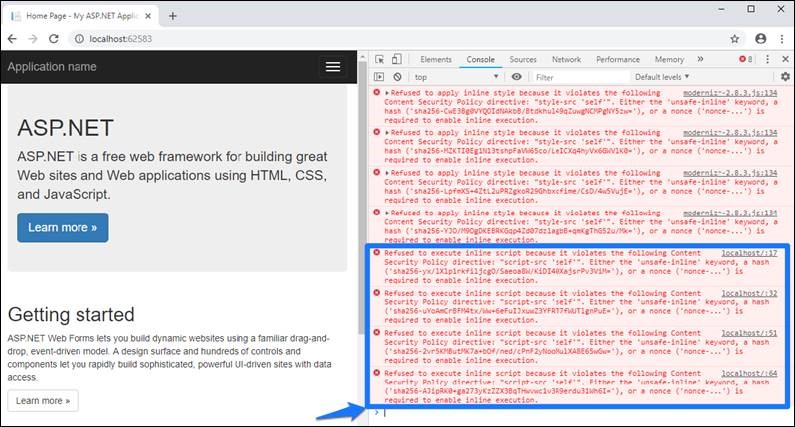
If the browser blocks a resource because it doesn’t comply with CSP, you will see this error in browser logs:
Refused to execute inline script because it violates the following Content Security Policy directive: “script-src ‘self'”. Either the ‘unsafe-inline’ keyword, a hash, or a nonce is required to enable inline execution.
How to prevent executing dynamic scripts with CSP?
Using unsafe-inline removes the error above (“Refuse to execute inline script“). However, it is not a secure way of whitelisting dynamically created scripts.
script-src 'self' 'unsafe-inline'Other than using unsafe-inline, it doesn’t seem like there is another way to whitelist dynamic scripts with CSP. There are a few open questions below if you want to keep posted about future updates on this topic.

I’ve been trawling the internet and trying all sorts of things to get around this problem. I can’t believe Microsoft can’t extend the framework to allow us to pass in a nonce value or perhaps even better, for the framework to automatically add a hash to the script blocks that it adds.
I’ve also been looking for a way to stop the site injecting the same script block into every page e.g. the code in the following script blocks could surely be included in the external WebForms.js file rather than being inline?
//
//
Hi Chris, did you check the solution in this page? I haven’t had a chance yet. I would appreciate if you share your comments if you try it out
https://stackoverflow.com/questions/54095422/how-to-whitelist-dynamically-created-scripts-in-a-webforms-project-using-csp-co?noredirect=1#comment95802412_54095422