CCS (Centralized Certificate Store) is feature we started using after IIS 8. It allows IIS to pick up website certificates from a network share instead of the local certificate store. For environments with multiple IIS servers, this is a feature that makes system administrators’ lives a lot easier. All you need to do is to add an IIS binding that points to CCS.
There are two steps to use CCS:
- Configure IIS to use CCS (a server-level setting in IIS)
- Add an IIS binding to your website. You can do it by
- Using IIS Manager OR
- Using PowerShell
1. Configure IIS to use CCS (Centralized Certificate Store)
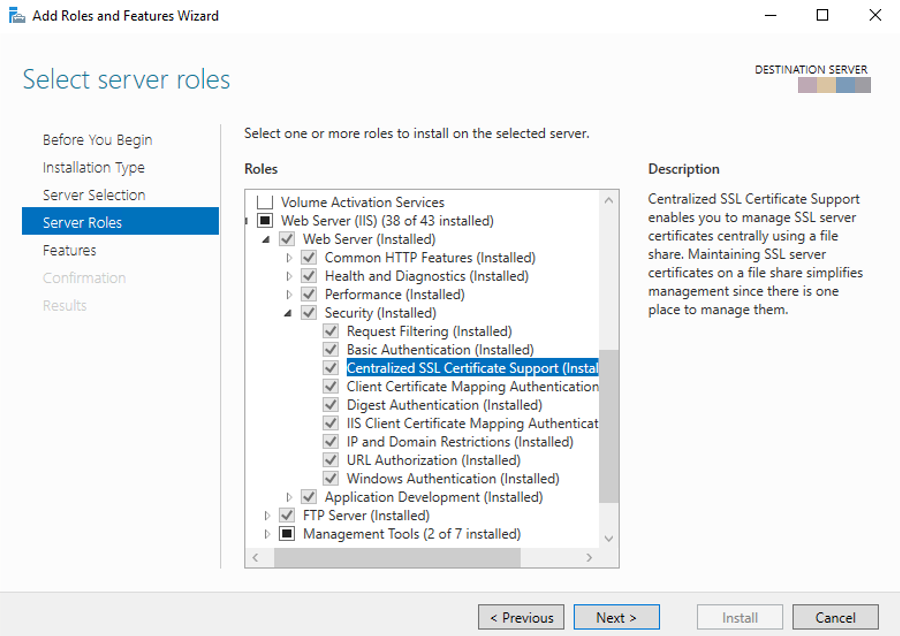
Install CCS feature via Server Manager:
After the installation:
- Go to IIS Manager
- Click on the server name
- Double click on “Centralized Certificates“
- Click “Edit Feature Settings” in the Action pane
- Fill out the fields:
- Enter a physical path (a network share or a local folder)
- Enter a username and password to access to this path
- If the certificates have private key password, specify it
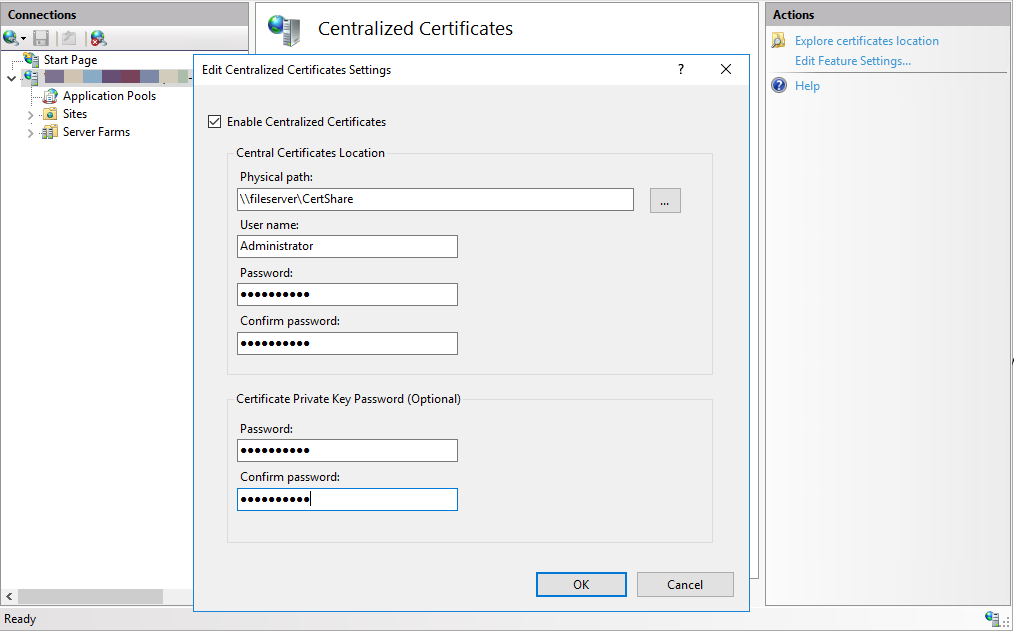
After saving the changes, IIS Manager reads the certificates from the path specified and populates the information about the certificates. This information is cached for better performance.
You may ask how IIS determines which certificate to use with which website? It uses the naming convention (<subject name of a certificate>.pfx). Examples:
- If the subject name is
www.contoso.com, IIS will look forwww.contoso.com.pfx - If IIS can’t find a match, it looks for a wildcard certificate in this name:
_.contoso.com.pfx - If you are using Subject Alternative Names (SANs), the file names should be
www.contoso1.com.pfxandwww.contoso2.com.pfx
Note: IIS stores the CCS configuration in this registry path: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\IIS\CentralCertProvider
After enabling CCS, are you seeing “This site is not secure” error? Check this post out: Fixed ERROR_INTERNET_SEC_CERT_REVOKED
2. Add an IIS binding that uses CCS
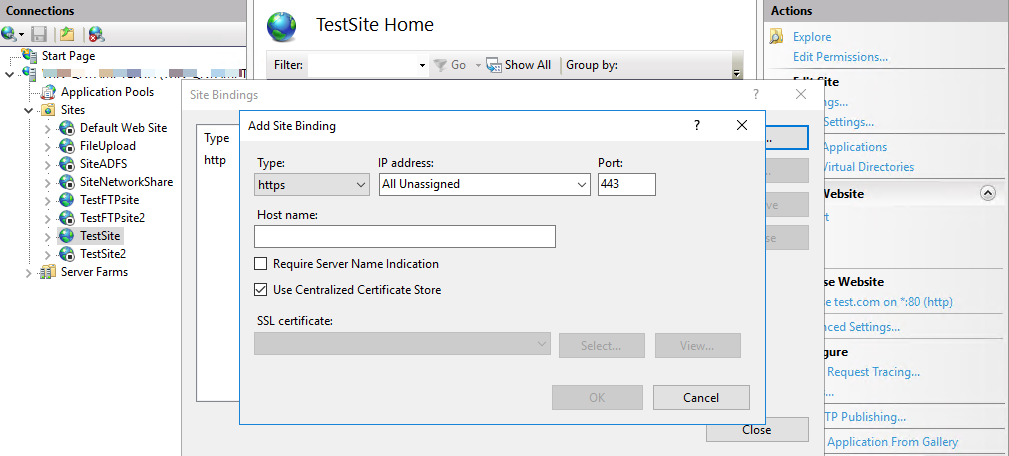
Add an IIS binding that uses CCS by using IIS Manager
- Go to IIS Manager
- Select the website
- Click “Bindings…” in the Action pane
- Click “Add“
- Select “https” from the “Type” list
- Select “Use Centralized Certificate Store“
Add an IIS binding that uses CCS by using PowerShell
In PowerShell, run the commands below.
New-WebBinding -Name "Default Web Site" -sslFlags 3 -Protocol https -IP * -Port 443 -HostHeader ("localhost")
New-Item -Path "IIS:\SslBindings\!443!localhost" -sslFlags 3 Please note that using only New-WebBinding won’t be enough because it won’t save this information to HTTP.SYS. You have to use New-Item command as well to add CCS binding to HTTP.SYS.
In order to check bindings, use netsh http show sslcert command.
The meanings of the sslFlags parameter:
| sslFlags | Description | Use CCS | Use SNI |
| 0 | SSL binding does not use SNI | 0 | 0 |
| 1 | SSL binding uses SNI | 0 | 1 |
| 2 | SSL binding does not use SNI, but uses Central Certificate Store (The hostname for certificate lookup is determined based on the binding information in Applicationhost.config) | 1 | 0 |
| 3 | SSL binding uses both SNI and Central Certificate Store | 1 | 1 |
Note: IIS stores the binding information in Registry. The path is HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\HTTP\Parameters\SslBindingInfo
After setting CCS up, you may want to redirect all HTTP requests to HTTPS. Here is how to do it: How to redirect HTTP requests to HTTPS by using IIS URL Rewrite

3 thoughts on “What is Centralized Certificate Store (CCS) and how to use it?”
Comments are closed.