Web applications use connection strings to find out what database to interact with which credentials and other configuration. For example, you can instruct your web application to use X database at the server with 192.168.1.100 IP address by using Z username and Y password.
For most applications, the connection strings are stored in web.config files. It means your IP address, database name, username, and password are stored as a clear text in a file. It may not be a problem for your Development server but it is definitely a security concern for your Production servers. This is where we need to encrypt these connection strings.
You can use Microsoft’s ASP.NET IIS Registration Tool (aspnet_regiis.exe) to encrypt and decrypt your connections strings. There are two scenarios to consider:
- Connection string encryption/decryption for a Single Server
- Connection string encryption/decryption for a Web Farm
Encrypt and decrypt connection strings for a single server
It’s relatively straightforward to encrypt and decrypt your connections strings if you are hosting your site in only one server. The steps below use the default key provider for encryption and decryption.
- Open Command Prompt as Administrator
- Go to this folder:
C:\Windows\Microsoft.NET\Framework\v4.0.30319 - Run the command below to encrypt the connection string in the web.config:
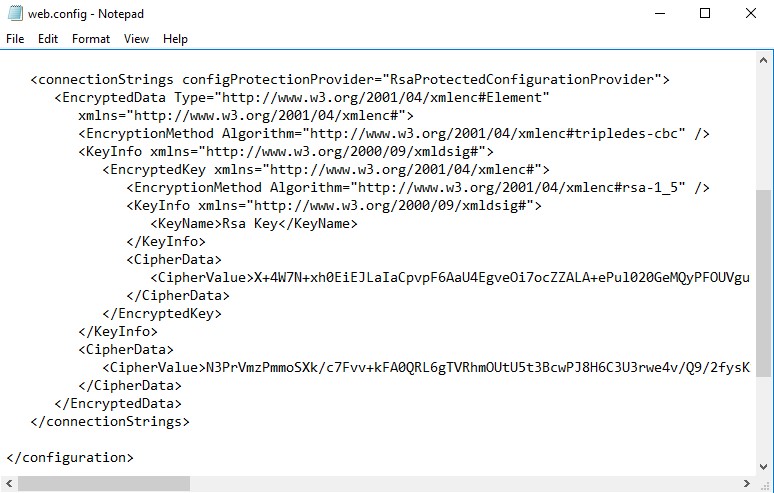
ASPNET_REGIIS -pef "connectionStrings" "D:\inetpub\wwwroot\applicationFolder" - Open the web.config and confirm that the connection string is encrypted
- Test the site and confirm that it is working
- Run the command below to decrypt the connection string:
ASPNET_REGIIS -pdf "connectionStrings" "D:\inetpub\wwwroot\applicationFolder" - Open the web.config and confirm that the connection string is decrypted
Here is the related Microsoft documentation: Encrypting and Decrypting Configuration Sections
Looking for a way to test connectivity between IIS server and database? Check this post out: How to test connectivity between a server and Oracle database?
For Web Farms
If you have a web farm, the method above won’t work because one IIS server won’t be able to decrypt the connection string encrypted by another IIS server. In order to make it work, you need to create and use an RSA key along with the RSA key provider so all servers would have the same key to decrypt connection strings.
Here are the high-level steps (Reference):
- Create an RSA key:
aspnet_regiis -pc "MyKeys" -exp - Grant access for application pool identity to this key:
aspnet_regiis -pa "MyKeys" "IIS AppPool\ApplicationPoolName" -full - Add RSA provider to the web.config:
<configuration>
<configProtectedData>
<providers>
<add name="MyProvider"
type="System.Configuration.RsaProtectedConfigurationProvider, System.Configuration, Version=2.0.0.0,
Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a,
processorArchitecture=MSIL"
keyContainerName="MyKeys"
useMachineContainer="true" />
</providers>
</configProtectedData>
</configuration>- Encrypt web.config by using the RSA provider:
aspnet_regiis -pe "connectionStrings" -app "/MyApplication" -prov "MyProvider" - Note: You can use the alternative syntax like the one we did for a single server scenario. Example:
ASPNET_REGIIS -pef "connectionStrings" "D:\inetpub\wwwroot\applicationFolder" -prov "MyProvider" - Open the web.config and confirm that the connection string is encrypted
- Test the site and confirm that it is working
- Try decrypting the web.config. Create a test.aspx file with the code below inside. Browse it to see the decrypted file
<%@ Page Language="VB" %>
<%@ Import Namespace="System.Configuration" %>
<script runat="server">
Public Sub Page_Load()
ConnectionStringsGrid.DataSource = ConfigurationManager.ConnectionStrings
ConnectionStringsGrid.DataBind()
End Sub
</script>
<html>
<body>
<form runat="server">
<asp:GridView runat="server" CellPadding="4" id="ConnectionStringsGrid" />
</form>
</body>
</html>
- Export the RSA key to the C drive:
aspnet_regiis -px "MyKeys" "c:\keys.xml" -pri - Copy this file to the second server in the web farm
- Import it in that server:
aspnet_regiis -pi "MyKeys" "c:\keys.xml" - Grant access to this key (same as Step 2)
- Test the application in the second server
- Remove c:\keys.xml file from all servers
Are you seeing “Failed to decrypt using provider RsaProtectedConfiguration Provider” error after this implementation? Check this post out: Solved: “Failed to decrypt using provider ‘RsaProtectedConfiguration Provider’. Error message from the provider: The RSA key container could not be opened”
