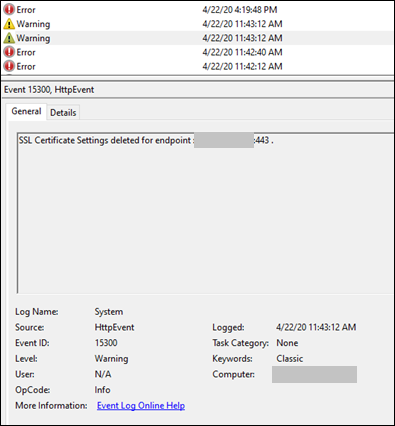
Every once in a while, I come across an issue where the IIS binding is deleted unexpectedly or the SSL certificate in the IIS binding is replaced or removed for some reason. In one of these cases, I saw “SSL Certificate Settings deleted for endpoint” warning message in Event Viewer:
Event ID 15300 (HttpEvent)
SSL Certificate Settings deleted for endpoint
Solution for “SSL Certificate Settings deleted for endpoint” warning
One of the root causes of this issue is the legacy SSL certificate hash property in the applicationHost.config file as mentioned here and here. Search for an entry similar to the one below and remove it.
<key path="LM/W3SVC/X">
<property id="5506" dataType="Binary" userType="1" attributes="None" value="oXiHOzFAMOF0YxIuI7soWvDFEzg=" />
</key>If it doesn’t work, here are a few more things to check:
- Check if there is an antivirus software in the server. Look for especially HIPS feature. Disable the antivirus and try to reproduce the issue
- Check if the site is using a wildcard certificate. This issue occurs when the wildcard certificate has been imported without marking the keys as exportable. In order to solve it, the affected certificate should be uninstalled and it should be imported back again with marking the keys as exportable
- Look for System Center Virtual Machine Manager Agent in the server. If it is enabled in the server, disable it and try to reproduce the issue (Reference)
- Another process might be using 443 port in the server (Example: Windows Admin Center. Check this post out: 503 Service Unavailable error related to Windows Admin Center)
- Check if insecure protocols are enabled. Registry settings are below. Disable these protocols if they are enabled and try to reproduce the issue
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Server
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Client
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Server
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\ClientIf it’s an Azure Cloud Service, the certificate might be controlled by the source code. In this case, you will need to have access to Visual Studio solution to implement a valid certificate.

1 thought on “SSL Certificate Settings deleted for endpoint (Event ID 15300)”
Comments are closed.