IIS uses bindings to determine which website a request should be redirected to. These bindings can use secured (https – mostly on port 443) or unsecured (http – mostly on 80) connection. While trying to add an https binding, I came across to this error: The request is not supported (Exception from HRESULT: 0x80070032).
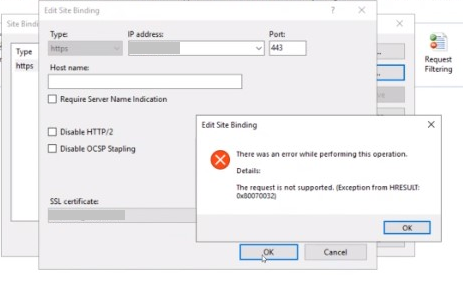
The screenshot from the IIS Manager:
There was an error while performing this operation
Details:
The request is not supported (Exception from HRESULT: 0x80070032)
We tried to add it by using this PowerShell command:
netsh http add sslcert ipport=[IP:port] appid="[APP ID]" certhash=[HASH] certstorename=MYIt gave a similar error:
SSL Certificate add failed, Error: 50
The request is not supported

The server OS version is Windows Server 2016. The important point is that this server went through in-place upgrade from Windows Server 2012 R2. The website never worked after the upgrade.
Oddly enough, Windows Update wasn’t working neither. It gave the following error when we wanted to check new updates.
Error(s): “We couldn’t connect to the update service. We’ll try again later, or you can check now. If it still doesn’t work, make sure you’re connected to the Internet.”
Solution for “The request is not supported (Exception from HRESULT: 0x80070032)” error
Since both secure binding and Windows Update were failing, we knew that it was worth to check TLS protocol settings. An issue in the TLS settings would cause binding issue in IIS. It would also prevent the machine communicate with Update servers.
If you are troubleshooting a similar issue, download and run IIS Crypto. Make sure TLS protocols and encryption algorithms are enabled.
Additionally, check if secure cipher suites are enabled. In the server I troubleshot, there was only one cipher suite active. This caused the both binding and Windows Update issues. We followed the steps below to use default cipher suite list in the server:
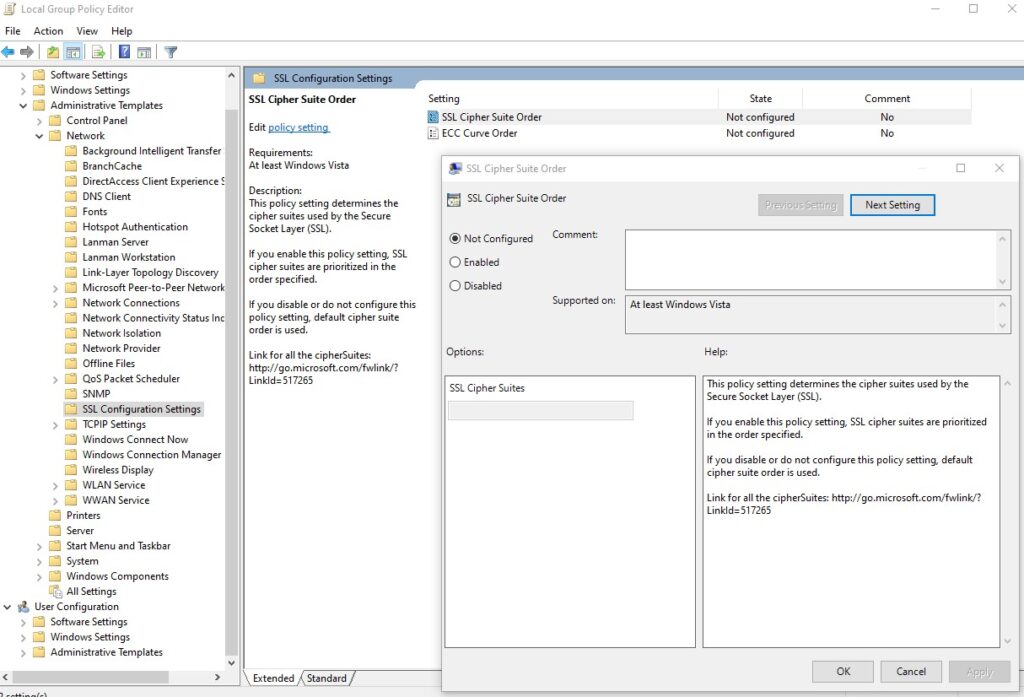
- Go to “Start > Run“. Enter: gpedit.msc
- In the left pane, expand “Computer Configuration > Administrative Templates > Network > SSL Configuration Settings“
- In the right pane, right click “SSL Cipher Suite Order” and choose “Edit”
- Save the text inside “SSL Chiper Suite” field to a Notepad for backup
- Select “Not Configured”
- Click “OK”
- Restart the server (gpupdate doesn’t enforce this setting. You should restart the server)
If the issue still occurs after the server restart, collect a network trace. Check if the TLS handshake is successful. If it is failing, have a look at this post: The missing Server Hello in TLS handshake (ERR_SSL_PROTOCOL_ERROR)
Check Event Viewer logs as well. There are probably Schannel errors. If there is an error with the 10013 code, check this post out: Schannel – The internal error state is 10013. For the 960 code: TLS fatal error code 20. The Windows SChannel error state is 960
